Learn the top tricks hackers use today and practical steps you can take right now to protect your website, devices, and data from common cyber attacks.
Introduction
Many people underestimate cyber threats — knowing the tricks hackers use is the first step to staying safe online. This post explains common attack patterns and defensive actions you can take immediately.
1. Phishing Emails and Fake Websites
One of the most common tricks hackers use is sending convincing phishing emails that lure victims to fake websites to steal credentials. Protect yourself by verifying sender addresses, checking URLs before clicking, and enabling two-factor authentication (2FA).

2. Social Engineering and Impersonation
A top social tactic among tricks hackers use is impersonating colleagues, tech support, or trusted services to extract information. Always verify identity through a separate channel and never share passwords or OTPs over chat or phone.

3. Weak or Reused Passwords
A basic but effective part of the tricks hackers use is exploiting weak or reused passwords across services. Use a password manager to create unique, strong passwords and enable 2FA on critical accounts.

4. Public Wi-Fi Eavesdropping
One wireless tricks hackers use is intercepting traffic on unsecured public Wi-Fi to capture login data. Avoid public Wi-Fi for sensitive tasks or use a reputable VPN to encrypt your connection.

5. Drive-by Downloads & Malicious Attachments
A frequent vector in the tricks hackers use is embedding malware in attachments or web downloads that run without clear consent. Don’t open unexpected attachments, keep your software updated, and scan downloads with antivirus software.

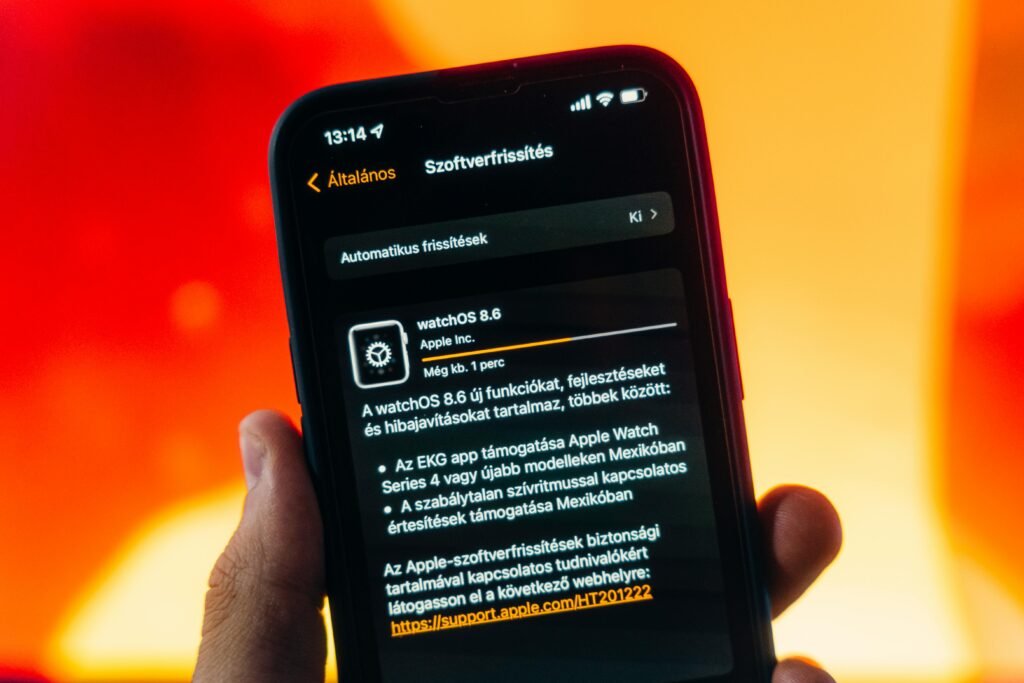
6. Outdated Software & Unpatched Vulnerabilities
Hackers exploit known vulnerabilities — one of the most reliable tricks hackers use is scanning for unpatched systems. Keep operating systems, plugins, and CMS (like WordPress) updated and apply security patches promptly.

7. Brute Force and Credential Stuffing
Automated attacks are among the tricks hackers use to guess passwords or reuse breached credentials. Protect accounts with rate limiting, account lockouts, and multi-factor authentication to reduce risk.
8. Malicious Mobile Apps & App Permissions Abuse
Some tricks hackers use involve malicious mobile apps that request excessive permissions to harvest data. Install apps only from trusted stores, review permissions, and uninstall apps you don’t use.
9. Supply-Chain and Third-Party Compromise
A sophisticated tactic among the tricks hackers use is compromising third-party services or libraries to reach many targets at once. Vet vendors, limit third-party access, and monitor unusual behavior from integrations.

10. Ransomware & Backup Manipulation
Ransomware is a destructive example of tricks hackers use to encrypt files and demand payment. Protect yourself with regular offline backups, segmented networks, and tested recovery procedures — and never pay ransoms lightly.

Practical Checklist: What to Do Today
Use this checklist to counter the tricks hackers use: enable 2FA, update software, use strong unique passwords, back up important data, scan for malware, restrict admin access, and train your team on phishing recognition.
Conclusion
Understanding the tricks hackers use helps you prioritize defenses and reduce risk. Cybersecurity is ongoing — stay vigilant, keep systems patched, and practice good digital hygiene.
